Share this
2022 Mid-Year Healthcare Data Breach Deep Dive
by Amanda Rogers, Marketing Content Writer, Protenus on August 1, 2022
As we're now midway through 2022, we thought we’d take a half-time pause to compare some data breach statistics in the healthcare space for the first half of 2022 to the first half of 2021. We'll also provide insight on how to proactively take a stand to better protect your patients and organization.
In this post, we’ll use the United States Department of Health and Human Services (HHS) public breach tool as well as data compiled by DataBreaches.net (“DataBreaches”) for Protenus.
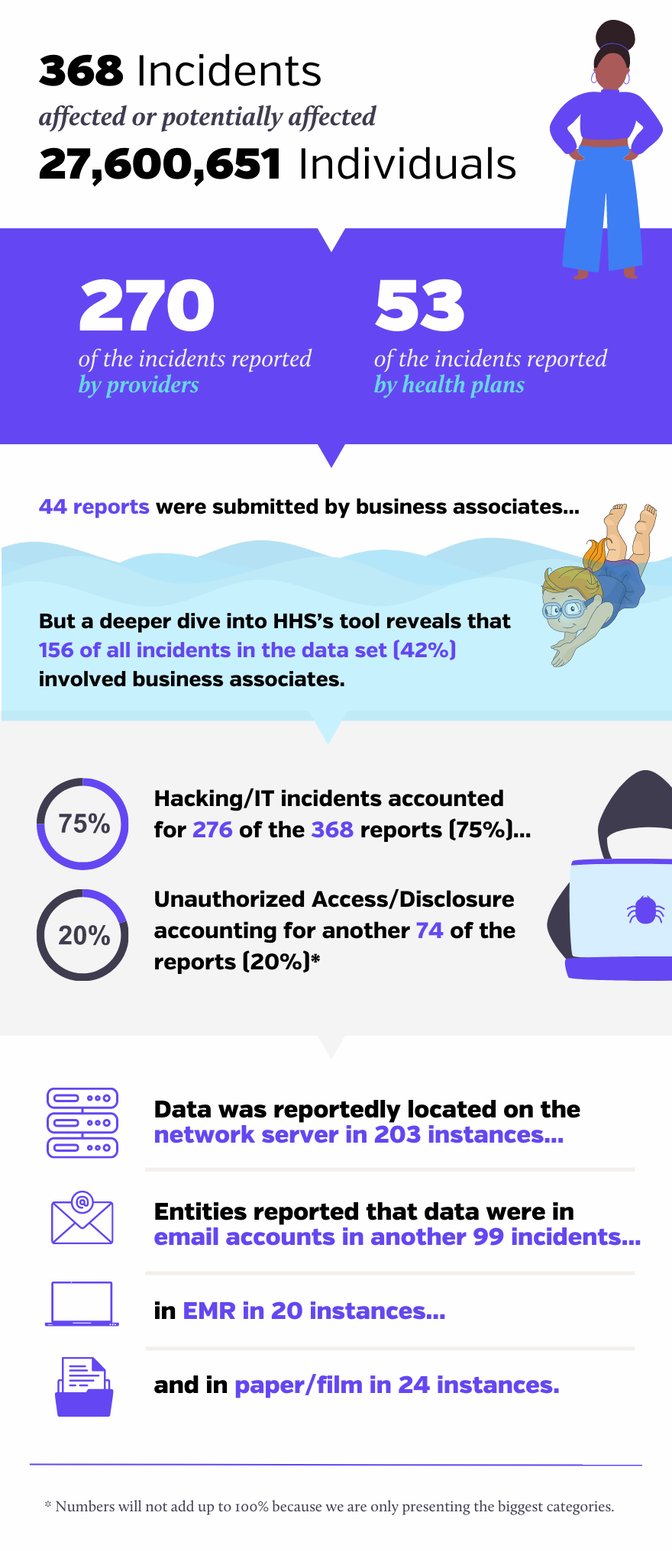
For January 1- June 30 in 2021, HHS’s breach tool included 368 reports. For that data set:
- The 368 incidents affected or potentially affected 27,600,651 individuals.
- 270 of the incidents were reported by providers and 53 were reported by health plans.
- 44 reports were submitted by business associates, but a deeper dive into HHS’s tool reveals that 156 of all incidents in the data set (42%) involved business associates.
- Hacking/IT incidents accounted for 276 of the 368 reports (75%), with Unauthorized Access/Disclosure accounting for another 74 of the reports (20%)[1].
- The 337 incidents affected or potentially affected 19,992,810 individuals.
- 244 of the incidents were reported by providers and 39 were reported by health plans.
- 54 incidents were reported by business associates but a deeper dive into HHS’s tool reveals that 123 of all incidents in the data set (36%) involved business associates.
- Hacking/IT incidents accounted for 269 of the 337 reports (80%), with Unauthorized Access/Disclosure accounting for another 50 of the reports (15%).
- Data was reportedly located on the network server in 163 instances. Entities reported that data were in email accounts in 86 instances, in EMR in 33 instances, and in paper/films in 26 instances.
.png?width=880&name=DISSENT%20DOE%20Infographic%202%20(2).png)
The numbers appear somewhat lower in 2022 so far, and proportionately so. But in addition to comparing HHS’s data for both years, we can also compare HHS’s data for the first half of 2022 to data compiled by DataBreaches.net. As reported in Protenus’ annual industry report, Breach Barometer, DataBreaches collects data from non-HIPAA entities as well as HIPAA-covered entities. DataBreaches also uses a different coding scheme to help differentiate employee errors from intentional employee wrongdoing and other types of unauthorized or inappropriate access.
For the first half of 2022, DataBreaches has already recorded 511 reports, fewer than the 580 reports it had compiled for the first half of 2021. The number of people affected is not available for many of the reports at this time, however.[3] For those reports where numbers were available, more than 24 million individuals have been impacted, down from the over 30 million recorded for the first half of 2021. As with HHS’s data, hacking incidents account for most reports in DataBreaches’ data set.
Don’t Pop the Champagne Just Yet?
While the numbers for the first half of 2022 are lower than 2021, don’t celebrate just yet. Numbers for the first half do not yet incorporate data from certain major incidents we know about. As but one example, one incident involving a business associate that was disclosed recently impacted more than 650 covered entities. Less than a handful of those entities have filed their reports yet with HHS (or if they have, HHS has yet to post them).
As noted in our Breach Barometer report, hackers made up a large portion of methods to breach. And ransomware attacks appear to be increasing again. Researchers have noted several new—and active — groups. Some of these groups are believed to involve members or affiliates of the former Conti enterprise. In addition to the emergence of new groups, there is also a shift occurring in methods. Some of the groups continue to use the double extortion model of ransomware, but others appear to be abandoning encrypting victims’ files in favor of just exfiltrating files and then trying to extort victims. The Cybersecurity & Infrastructure Security Agency (CISA) also recently issued an advisory about North Korean state-sponsored actors using Maui ransomware to target the healthcare and public health sector.
Along with ransomware attacks, insider events pose a significant risk to data security in healthcare as employees can fall prey to phishing attacks or engage in other behaviors that increase the risk of a privacy or security breach. There are also bad actors actively seeking to actively seeking to purchase employees’ login credentials to intended victim entities.
Take a Stand, Be Proactive
Protenus can help hospitals and healthcare organizations transition to a proactive stance in protecting patient privacy. By harnessing the power of artificial intelligence (AI) to audit up to 100% of system accesses, healthcare organizations can detect inappropriate or suspicious user behavior earlier, mitigating or eliminating risk and keeping their patients and organization safer. With an AI-powered solution, healthcare organizations can catch and contain breaches 27% faster and their cost of a data breach is $3.81 million lower on average than organizations without such technology, according to IBM's 2021 Cost of a Data Breach Report.
To learn more about Protenus' AI-powered Patient Privacy Monitoring solution, schedule a demo with our team today.
[1] Numbers will not add up to 100% because we are only presenting the biggest categories.
[2] Note: There are often lags before HHS adds items to its site, so the numbers for this part of the report may increase when we get final figures for the first half of this year.
[3] While entities provide numbers to HHS with their reports, DataBreaches cannot mandate that non-HIPAA entities disclose the number affected when they issue press releases or substitute notices. As a result, it may not be until many months later, if at all, when DataBreaches gets numbers for some incidents.
Share this
- December 1, 2024 (3)
- November 1, 2024 (1)
- October 1, 2024 (2)
- September 1, 2024 (1)
- August 1, 2024 (1)
- July 1, 2024 (1)
- June 1, 2024 (1)
- May 1, 2024 (1)
- March 1, 2024 (2)
- February 1, 2024 (3)
- January 1, 2024 (1)
- December 1, 2023 (1)
- November 1, 2023 (3)
- October 1, 2023 (3)
- September 1, 2023 (1)
- August 1, 2023 (1)
- July 1, 2023 (2)
- April 1, 2023 (1)
- March 1, 2023 (1)
- February 1, 2023 (1)
- December 1, 2022 (3)
- November 1, 2022 (3)
- October 1, 2022 (1)
- September 1, 2022 (1)
- August 1, 2022 (2)
- June 1, 2022 (4)
- May 1, 2022 (5)
- April 1, 2022 (1)
- March 1, 2022 (4)
- February 1, 2022 (3)
- November 1, 2021 (2)
- October 1, 2021 (3)
- September 1, 2021 (3)
- August 1, 2021 (3)
- July 1, 2021 (4)
- June 1, 2021 (2)
- May 1, 2021 (2)
- April 1, 2021 (2)
- March 1, 2021 (5)
- February 1, 2021 (1)
- January 1, 2021 (1)
- December 1, 2020 (1)
- November 1, 2020 (2)
- October 1, 2020 (2)
- September 1, 2020 (3)
- August 1, 2020 (2)
- July 1, 2020 (2)
- June 1, 2020 (6)
- May 1, 2020 (3)
- April 1, 2020 (4)
- March 1, 2020 (2)
- February 1, 2020 (4)
- January 1, 2020 (2)
- December 1, 2019 (2)
- November 1, 2019 (1)
- October 1, 2019 (1)
- September 1, 2019 (1)
- August 1, 2019 (1)
- June 1, 2019 (1)
- April 1, 2019 (1)
- February 1, 2019 (1)
- January 1, 2019 (1)
- December 1, 2018 (2)
- November 1, 2018 (2)
- October 1, 2018 (2)
- September 1, 2018 (3)
- August 1, 2018 (1)
- July 1, 2018 (2)
- June 1, 2018 (2)
- May 1, 2018 (1)
- April 1, 2018 (1)
- March 1, 2018 (2)
- February 1, 2018 (6)
- January 1, 2018 (2)
- September 1, 2017 (2)
- August 1, 2017 (2)
- June 1, 2017 (2)
- May 1, 2017 (1)
- April 1, 2017 (1)
- March 1, 2017 (2)
- February 1, 2017 (5)
- January 1, 2017 (2)
- December 1, 2016 (3)
- November 1, 2016 (5)
- October 1, 2016 (4)
- September 1, 2016 (8)
- August 1, 2016 (4)
- July 1, 2016 (4)
Subscribe by email
You May Also Like
Conserving Resources with Compliance Analytics: A 5-Step Implementation Guide

Enabling Greater Healthcare Efficiency with Protenus AI Technology

.png?width=1000&height=140&name=Bluesight%20%2B%20Protenus%20Logo%20%20(1).png)

