Share this

Insider-Wrongdoing in the Healthcare Sector
by Michelle Del Guercio on August 16, 2023
On June 8, the Health Sector Cybersecurity Coordination Center (“HC3”) published Types of Cyber Threat Actors That Threaten Healthcare. In that publication, they identify five basic types of insider threats:
- careless or negligent workers
- malicious insiders
- inside agents
- disgruntled employees
- third parties
In 2016, when Protenus and DataBreaches first began collaborating on collecting and analyzing data from reported breaches involving health data, we focused on what is often called the “insider threat” by breaking it down into two categories: human error or breaches due to accidents, which we called “insider-error,” and breaches due to intentional wrongdoing by employees or contractors, which we called “insider-wrongdoing.” Because we have used this categorization for the last few years, we thought this might be a good time to do a look-back and see if, using that framework, insider-wrongdoing reports appear to have increased, decreased or stayed approximately the same over the years. Thus, this blog post will focus specifically on the insider-wrongdoing category of data.
Based on data compiled between 2016 and 2022 (see Table 1), 371 incidents were reported that fit the definition of insider-wrongdoing. For the 283 insider-wrongdoing incidents for which we had data, more than 2.5 million patient records were involved.
| Year | NUMBER of INCIDENTS | NUMBER of RECORDS per INCIDENT |
| 2016 | 91 | 412,469 (72) |
| 2017 | 70 | 893,978 (57) |
| 2018 | 45 | 386,469 (29) |
| 2019 | 36 | 136,572 (28) |
| 2020 | 45 | 241,128 (31) |
| 2021 | 37 | 309,031 (31) |
| 2022 | 47 | 150,325 (35) |
| Totals: | 371 | 2,529,972 |
Table 1: Insider Wrong-doing 2016-2022
The number in parentheses indicates the number of reports for which we had the number of records compromised. So far in 2023, DataBreaches.net has tabulated 12 insider-wrongdoing reports affecting 35,981 records for the 11 incidents for which we have numbers1.
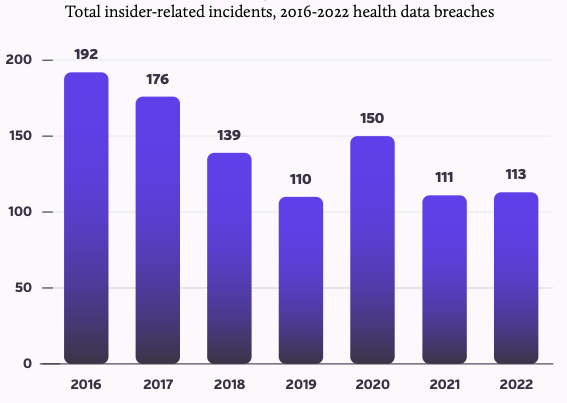
2022 Healthcare Data Breaches
With 113 total insider incidents (which includes both insider error and insider wrongdoing) recorded throughout 2022, insiders were responsible for 12% of the total number of healthcare breaches in 2022. Of those reported in 2022, 66 were caused by insider error, and 47 were caused by insider wrongdoing. (Source: 2023 Breach Barometer)
Insider Wrongdoing is a Constant Threat
As shown in Table 1, after 2016 and 2017 high volumes, there were fewer insider-wrongdoing cases publicly reported each year, but not in any consistent downward pattern. The post-2017 decrease cannot be explained by any overall decrease in the number of reported incidents because the overall number of breach reports increased each year, with yearly counts more than doubling by 2022. The increasing number of reports annually but decreasing numbers of insider-wrongdoing cases explains, in large part, why insider-wrongdoing has accounted for a smaller percentage of all reports in recent years.
Not only did the number of insider-wrongdoing reports decrease after 2017, but the percent of total records accounted for by insider-wrongdoing cases decreased – and decreased even more than the decreased percent of total incidents. In recent years, insider-wrongdoing reports have accounted for less than 1% of all records breached each year. When one considers the tremendous uptick in ransomware attacks and their associated hacked records, the significant decrease in percentage seems easily explained. But the short version of it all is that there was no consistent trend over the past six years for frequency of insider-wrongdoing reports or number of records compromised by insider-wrongdoing reports.
In the meantime, civil enforcement of some insider-wrongdoing cases continues, although generally not with any great speed. As one example, HHS recently settled a complaint with a hospital where the incident involved 23 security guards accessing the medical records of 419 patients in 2018.
So Where Are We?
Insider threat remains a concern in all sectors, and the healthcare sector is no different in that respect. Unlike other sectors where insider wrongdoing may result in fraudulent purchases on someone’s account or intellectual property theft, the risk of harm in the healthcare sector strikes us as much more serious, and personal.
For many reasons, then, we believe, but cannot prove, that insider-wrongdoing is a significantly under-reported problem in the healthcare sector. A financially motivated employee who accepts a bribe from a ransomware group may be responsible for healthcare systems being encrypted, patient records corrupted, and urgently needed healthcare being delayed or diverted. An employee with a grudge against someone may decide to “anonymously” post embarrassing medical information about them on social media. An employee who gets annoyed by all the phishing drills and exercises may decide that it’s all hype and they then just click on links in their incoming email and thereby introduce malware to the system. While financial motivation is the predominant motivation in most sectors, healthcare fraud cases that may involve many patients’ information being misused do not always seem to appear on HHS’s public breach tool, such as when a corrupt entity creates false medical record notes for patients to support fraudulent billing of insurers. Hundreds or more than a thousand patients may have their protected health information misused to support the fraud, but the entity may not report that as a breach to HHS.
On average breaches are not identified for 96 days (from incident occurrence to discovery). - 2023 Breach Barometer Report
All too often, patient record breaches go unnoticed for extended lengths of time. On average breaches are not identified for 96 days (from incident occurrence to discovery). Human efforts alone cannot efficiently or accurately monitor the amount of data hospitals produce daily to adequately identify and report suspicious incidents. These delays can have a major negative impact on the healthcare organization, which may include reputational damage leading to loss of new and repeat patients, significant financial impacts due to legal and compliance consequences and additional workload on an already stressed workforce. Healthcare leaders must continue to remain vigilant in their approach to preventing patient breaches and protecting patient data. A proactive approach, combining processes and AI-driven Patient Privacy Monitoring technology, helps mitigate risk to the healthcare organization and its patients. Only when a healthcare organization can fully understand their overall risk of a breach - from all types of threats, can they more effectively allocate resources, and deploy technology and processes to aid in the auditing, monitoring and protection of every patient’s record.
Thanks to DataBreaches.net for help with data analyses for this post!
1Methodology Assumptions and Source of Data: Our methodology includes the analysis of data reported to the Department of Health and Human Services (HHS). The HHS public breach tool only includes breaches affecting 500 or more patients. As such, we do not see all the cases where an employee who is curious snoops on a friend’s or relative’s or celebrity’s medical records with no intention of doing them harm, for example. Those cases are civil violations of HIPAA and should be reported to HHS, but even if they were publicly available like larger incidents, HHS’s manner of coding incidents would likely result in them being coded as “unauthorized access or disclosure.” HHS’s coding could also cover an insider error such as emailing a file to the wrong party, so we cannot just use frequency counts from HHS’s “unauthorized access or disclosure” data for “insider-wrongdoing.”
Share this
- December 1, 2024 (3)
- November 1, 2024 (1)
- October 1, 2024 (2)
- September 1, 2024 (1)
- August 1, 2024 (1)
- July 1, 2024 (1)
- June 1, 2024 (1)
- May 1, 2024 (1)
- March 1, 2024 (2)
- February 1, 2024 (3)
- January 1, 2024 (1)
- December 1, 2023 (1)
- November 1, 2023 (3)
- October 1, 2023 (3)
- September 1, 2023 (1)
- August 1, 2023 (1)
- July 1, 2023 (2)
- April 1, 2023 (1)
- March 1, 2023 (1)
- February 1, 2023 (1)
- December 1, 2022 (3)
- November 1, 2022 (3)
- October 1, 2022 (1)
- September 1, 2022 (1)
- August 1, 2022 (2)
- June 1, 2022 (4)
- May 1, 2022 (5)
- April 1, 2022 (1)
- March 1, 2022 (4)
- February 1, 2022 (3)
- November 1, 2021 (2)
- October 1, 2021 (3)
- September 1, 2021 (3)
- August 1, 2021 (3)
- July 1, 2021 (4)
- June 1, 2021 (2)
- May 1, 2021 (2)
- April 1, 2021 (2)
- March 1, 2021 (5)
- February 1, 2021 (1)
- January 1, 2021 (1)
- December 1, 2020 (1)
- November 1, 2020 (2)
- October 1, 2020 (2)
- September 1, 2020 (3)
- August 1, 2020 (2)
- July 1, 2020 (2)
- June 1, 2020 (6)
- May 1, 2020 (3)
- April 1, 2020 (4)
- March 1, 2020 (2)
- February 1, 2020 (4)
- January 1, 2020 (2)
- December 1, 2019 (2)
- November 1, 2019 (1)
- October 1, 2019 (1)
- September 1, 2019 (1)
- August 1, 2019 (1)
- June 1, 2019 (1)
- April 1, 2019 (1)
- February 1, 2019 (1)
- January 1, 2019 (1)
- December 1, 2018 (2)
- November 1, 2018 (2)
- October 1, 2018 (2)
- September 1, 2018 (3)
- August 1, 2018 (1)
- July 1, 2018 (2)
- June 1, 2018 (2)
- May 1, 2018 (1)
- April 1, 2018 (1)
- March 1, 2018 (2)
- February 1, 2018 (6)
- January 1, 2018 (2)
- September 1, 2017 (2)
- August 1, 2017 (2)
- June 1, 2017 (2)
- May 1, 2017 (1)
- April 1, 2017 (1)
- March 1, 2017 (2)
- February 1, 2017 (5)
- January 1, 2017 (2)
- December 1, 2016 (3)
- November 1, 2016 (5)
- October 1, 2016 (4)
- September 1, 2016 (8)
- August 1, 2016 (4)
- July 1, 2016 (4)
Subscribe by email
You May Also Like
Conserving Resources with Compliance Analytics: A 5-Step Implementation Guide

Enabling Greater Healthcare Efficiency with Protenus AI Technology

.png?width=1000&height=140&name=Bluesight%20%2B%20Protenus%20Logo%20%20(1).png)
